What Is The Medusa Ransomware Gang Phishing Campaigns About?
The topic of the day is Medusa Ransomware Gang Phishing Campaigns!
The Medusa ransomware group is quickly becoming a major player in the ransomware world for 2025.
They don’t just lock up data – they hit businesses with double extortion, threatening to leak sensitive information if they don’t get paid. That’s a nightmare for any company worried about its reputation.
Medusa makes things even worse by offering its ransomware tools to affiliates. So, attacks keep popping up everywhere, thanks to their Ransomware-as-a-Service (RaaS) model.
All of this just shows how important it is for organizations to build strong security defenses and have clear plans to stop ransomware before it spreads.
So, if you want to know about the Medusa Ransomware Gang Phishing Campaigns and learn about how to mitigate the risks, keep reading!
Who Is The Medusa Ransomware Gang?

Medusa has exploded onto the ransomware scene since 2023, racking up hundreds of victims and landing in the top ten list of ransomware actors.
At first, only the Medusa group itself ran attacks – everything stayed in-house. But things changed when they rolled out an affiliate model, letting outside partners launch attacks of their own.
Even with affiliates in the mix, though, the main Medusa crew still controls all ransom negotiations.
Nobody knows exactly where the Medusa group is based, but there’s a strong case for Russia or one of its allies.
The group steers clear of targets in Russia and the Commonwealth of Independent States, and they’re active on Russian-language dark web forums like RAMP.
That kind of behavior usually points to actors operating in or around Russia.
Don’t confuse Medusa with MedusaLocker or the Medusa mobile malware – they’re separate threats.
Medusa stands alone; there’s no real evidence tying them to any other cybercrime group, and their ransomware code is unique.
So far, nobody has found overlaps with other ransomware-as-a-service tools.
There’s some chatter linking Medusa to an eCrime group called “Frozen Spider.” The details are a bit murky.
However, it looks like Frozen Spider uses Medusa ransomware for what’s known as “big game hunting” – going after large organizations in hopes of scoring bigger ransom payouts.
Medusa Ransomware Gang Phishing Campaigns Targets
The Medusa ransomware group doesn’t really stick to one industry – they go after all sorts of targets. Hospitals, schools, tech companies, factories, law firms, government agencies – you name it.
Big names like the Minneapolis Public School District and Toyota Financial Services have already landed on their hit list, according to Check Point.
Medusa likes to hit small and mid-sized businesses, especially in fields where sensitive data, a lot of digital infrastructure, and staying online really matter.
When these companies fall prey to such attacks, they’re more likely to pay up fast, just to get back to business and keep their data safe.
You see Medusa’s impact worldwide – victims have popped up in more than 45 countries, including the US, Canada, Australia, Germany, Italy, and the UK. Actually, the UK stands out. Medusa pulls off a lot more attacks there than in most places.
For instance, in the first quarter of 2025, they were behind 9% of all reported ransomware victims in the UK. Globally, they’re responsible for just 2%. So, their presence in the UK is way above average.
Medusa Ransomware Gang Phishing Campaigns Characteristics
Here are some of the major characteristics of the Medusa Ransomware Gang Phishing Campaigns that you need to learn about:
- Targeted Platforms: Hackers are going after both personal and business accounts on Gmail and Outlook lately.
- Delivery Methods: They send out sneaky emails with links or attachments that look totally normal, but they’re loaded with malware.
- Social Engineering: Sometimes they dangle offers that seem way too good to be true, or they’ll create a sense of urgency with business-related messages, hoping to trick people into giving up their login info or running harmful scripts.
Recent High-Profile Targets & Impacts Of Medusa Ransomware Gang Phishing Campaigns
Since it showed up, the Medusa group has hit more than 300 organizations, and not just random ones – these are places that keep things running, according to CISA.
Take healthcare, for example. Symantec pointed out a recent attack on a U.S. healthcare organization. That’s not just annoying – it’s dangerous.
Tech hasn’t been spared either. Back in February 2026, Medusa went after Comcast and said it grabbed over 800 GB of data. That’s a huge haul.
And schools? They’ve been dragged in, too. Medusa targeted the Minneapolis Public School District and, after officials said no to a $1 million ransom, the group leaked sensitive student psychological reports. That kind of exposure sticks.
How Does The Medusa Ransomware Gang Phishing Campaigns Work?
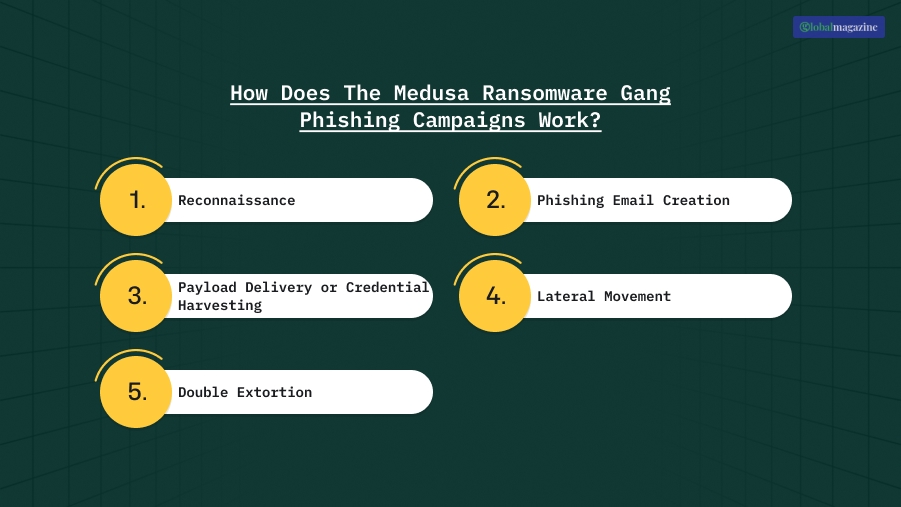
Here’s how the Medusa ransomware gang usually runs their phishing campaigns or attacks:
1. Reconnaissance
First, they do their homework. They dig into your organization, figure out who’s who – maybe a finance lead, an IT admin, someone in procurement.
They snoop around for details, like how your email addresses are formatted, who’s connected on LinkedIn, and which vendors you work with. Anything they can find that makes their job easier.
2. Phishing Email Creation
Next, they write the phishing emails. These aren’t random spam – they’re built to look legit, based on things your team actually deals with.
Maybe it’s an invoice from a real vendor, a request to check out a shared document, a fake Zoom invite, or a cloud login alert.
Basically, they tweak every message in such a way that it matches the target’s job
3. Payload Delivery or Credential Harvesting
Thirdly comes the real punch – the credential harvesting. The email either has a file loaded with malware – usually a macro-laced doc – or it points you to a fake login page that looks just like Microsoft 365 or Google Workspace. Either way, they’re after your credentials or a way in.
4. Lateral Movement
If they get what they want, they start moving laterally through your network. They grab more access, knock out security tools, and set up everything they need for the big hit. And this way, they are able to lock your files.
5. Double Extortion
Finally, there’s something that most people are unaware of – double extortion! Yes, you read that right!
They don’t just stop at encryption. Before they scramble your data, they steal sensitive files. When they finally demand ransom, they threaten to leak your data if you don’t pay – backups or no backups.
That’s the playbook. Encryption is just the last card they play.
Read Also: What are The Most Relevant Cybersecurity Questions to Ask Your IT Department?
How To Mitigate The Medusa Ransomware Gang Phishing Threats?
CISA just shared some quick steps for organizations to deal with Medusa ransomware threats:
- First, patch your systems – make sure your operating systems, software, and firmware are all up to date, and do this on a schedule that fits your risk level.
- Next, split up your network so that if one device gets hit, the attack can’t spread easily to others.
- Finally, they block strange or untrusted network traffic, especially anything trying to access your internal systems from the outside.
CISA also put out a full list of ways to cut down your chances of falling prey to Medusa Ransomware gang phishing campaigns or similar ransomware attacks:
- Encrypt all your backup data and make it so nobody can change or delete it.
- Cover every part of your organization’s data.
- Have a plan to keep multiple backup copies of important data and servers.
- Make sure you’re storing those backups somewhere safe, physically separated from your main systems.
- Keep offline backups, and check regularly that you can actually restore from them.
Apart from the ones that I have already mentioned above, make sure every account with a password – services, admins, or domain admins – follows NIST’s standards.
Turn on multifactor authentication wherever you can, especially for webmail, VPNs, and any accounts that touch your critical systems.

























